In the volatile world of cryptocurrency markets, detecting anomalies is crucial for risk management, fraud prevention, and trading strategy optimization. Abnormal price movements, unusual transaction patterns, and market manipulation schemes can significantly impact investments and market integrity. Neural networks have emerged as powerful tools for identifying these anomalies due to their ability to learn complex patterns from high-dimensional data. This comprehensive guide will walk you through the process of implementing neural network-based anomaly detection systems specifically designed for cryptocurrency markets.
Neural networks can identify complex anomaly patterns in cryptocurrency data that traditional statistical methods might miss
Overview of Neural Networks in Financial Anomaly Detection
Neural networks have revolutionized anomaly detection in financial markets by providing sophisticated pattern recognition capabilities that surpass traditional statistical methods. In cryptocurrency markets, where volatility and manipulation are common, these advanced models offer significant advantages.
Why Neural Networks Excel at Cryptocurrency Anomaly Detection
Cryptocurrency markets present unique challenges for anomaly detection due to their 24/7 operation, high volatility, and susceptibility to manipulation. Neural networks are particularly well-suited for this domain for several reasons:
Handling Non-Linear Relationships
Cryptocurrency price movements often exhibit non-linear relationships that traditional statistical methods struggle to capture. Neural networks excel at modeling these complex patterns through their hierarchical structure and non-linear activation functions.
Adaptability to Market Conditions
As market conditions evolve, neural networks can be retrained to adapt to new patterns. This adaptability is crucial in cryptocurrency markets, where conditions can change rapidly due to regulatory announcements, technological developments, or market sentiment shifts.
Feature Learning
Deep learning models can automatically learn relevant features from raw data, reducing the need for manual feature engineering. This capability is valuable when dealing with the multidimensional nature of cryptocurrency data, which includes price, volume, blockchain metrics, and social sentiment.
Handling High-Dimensional Data
Cryptocurrency anomaly detection often involves analyzing multiple data streams simultaneously. Neural networks can effectively process high-dimensional inputs, making them ideal for integrating diverse data sources.
Types of Anomalies in Cryptocurrency Markets
Before implementing a neural network for anomaly detection, it’s important to understand the types of anomalies you might encounter in cryptocurrency markets:
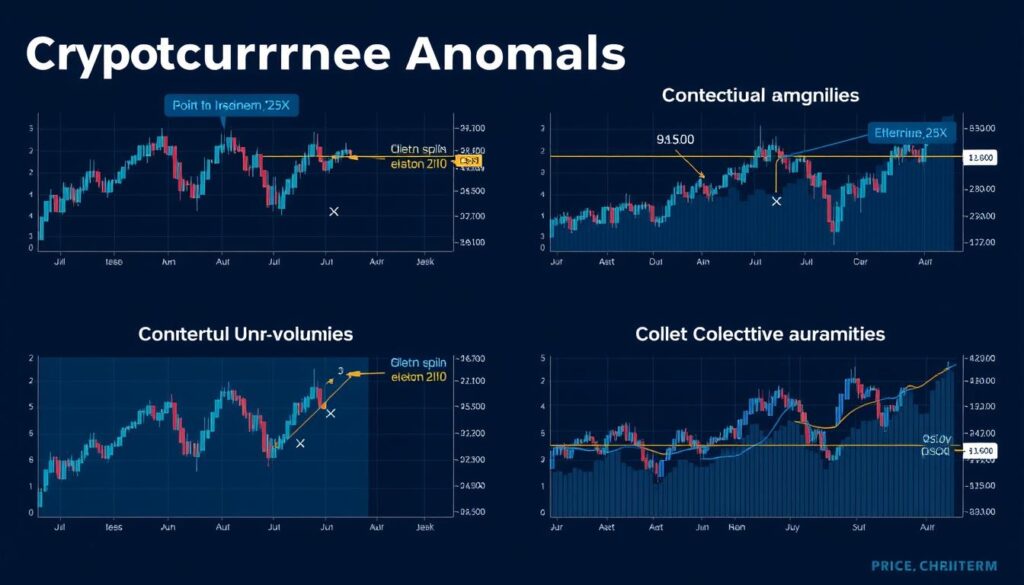
Visual representation of different types of anomalies in cryptocurrency price and volume data
Data Collection and Preprocessing for Cryptocurrency Anomaly Detection
Effective anomaly detection begins with comprehensive data collection and preprocessing. The quality and diversity of your data will significantly impact the performance of your neural network models.
Essential Data Sources
A robust cryptocurrency anomaly detection system should incorporate data from multiple sources:
Market Data
- Price (OHLCV – Open, High, Low, Close, Volume)
- Order book depth
- Trade-by-trade data
- Liquidity metrics
- Volatility indicators
Blockchain Data
- Transaction volumes
- Network hash rate
- Active addresses
- Transaction fees
- Block size and time
- Wallet activity patterns
External Data
- Social media sentiment
- News events
- Regulatory announcements
- Macroeconomic indicators
- Related asset prices
- Exchange outages/issues
Data Collection APIs and Resources
Several APIs and services provide access to cryptocurrency data:
| Data Type | Recommended APIs | Data Frequency | Cost | Features |
| Market Data | CoinAPI, CryptoCompare, Binance API | Millisecond to daily | Free tiers available, premium plans from $79/month | Historical OHLCV, real-time websockets, order book data |
| Blockchain Data | Blockchair, Etherscan API, Glassnode | Block-by-block, daily aggregates | Free tiers with rate limits, premium from $49/month | On-chain metrics, wallet analysis, network health |
| Social/News Data | Santiment, LunarCRUSH, Twitter API | Real-time to hourly | Free tiers, premium from $30/month | Sentiment analysis, social volume, trending topics |
| Combined Datasets | Kaiko, Amberdata, CoinMetrics | Varies by metric | Enterprise pricing (contact sales) | Integrated market and on-chain data, institutional grade |
Access Quality Cryptocurrency Data
Start building your anomaly detection system with comprehensive cryptocurrency data from CryptoCompare. Their API offers market data across multiple exchanges with both free and premium tiers.
Data Preprocessing Techniques
Raw cryptocurrency data requires careful preprocessing before it can be used for neural network training:
Handling Missing Data
Cryptocurrency markets operate 24/7, but data collection systems may experience outages. Techniques for handling missing data include:
- Forward filling (using the last known value)
- Interpolation (linear, polynomial, or spline)
- Using the mean/median of surrounding values
- More sophisticated methods like MICE (Multivariate Imputation by Chained Equations)
Normalization and Scaling
Neural networks perform better when input features are on similar scales. Common scaling techniques include:
- Min-Max Scaling: Transforms features to a range between 0 and 1
- Standardization: Transforms features to have zero mean and unit variance
- Robust Scaling: Uses quantiles instead of min-max, making it robust to outliers
- Log Transformation: Useful for highly skewed data like trading volume
Feature Engineering
While neural networks can learn features automatically, engineered features can improve performance:
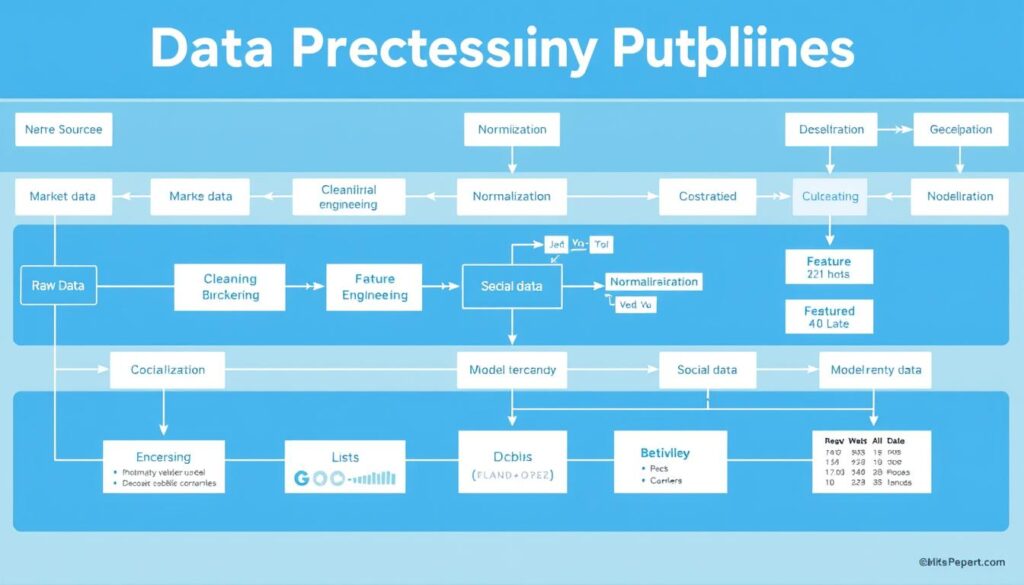
Data preprocessing pipeline for cryptocurrency anomaly detection systems
Sample Dataset Structure
Here’s an example of a preprocessed dataset structure for cryptocurrency anomaly detection:
timestamp,price_close,price_open,price_high,price_low,volume,rsi_14,bollinger_upper,bollinger_lower,
macd,social_sentiment,active_addresses,transaction_count,is_anomaly
2023-01-01T00:00:00Z,16500.25,16498.75,16525.50,16475.00,1250.5,45.2,16800.75,16200.25,-5.2,0.65,950000,125000,0
2023-01-01T01:00:00Z,16525.50,16500.25,16550.00,16490.00,1300.2,46.5,16825.50,16225.50,-4.8,0.68,955000,126000,0
2023-01-01T02:00:00Z,16700.00,16525.50,16725.00,16520.00,2500.8,52.3,16850.25,16250.75,-2.1,0.85,980000,145000,1
...
This dataset includes price data, technical indicators, social sentiment, and blockchain metrics, along with a binary label indicating whether each data point represents an anomaly (typically labeled by domain experts or using unsupervised techniques).
Neural Network Model Selection for Cryptocurrency Anomaly Detection
Selecting the appropriate neural network architecture is crucial for effective anomaly detection in cryptocurrency markets. Different architectures excel at capturing different types of patterns and anomalies.
Supervised vs. Unsupervised Approaches
Anomaly detection can be approached in two primary ways:
Supervised Learning
- Advantages: Higher precision, can target specific known anomaly types
- Requirements: Labeled dataset with examples of normal and anomalous behavior
- Use case: When you have historical examples of specific anomalies (e.g., known pump-and-dump schemes)
- Common models: CNN, LSTM, Transformer-based networks
Unsupervised Learning
- Advantages: Can detect novel, previously unseen anomalies
- Requirements: Only normal data is needed for training
- Use case: When labeled anomaly data is scarce or when looking for new types of anomalies
- Common models: Autoencoders, GANs, Self-Organizing Maps
Neural Network Architectures for Cryptocurrency Anomaly Detection
Several neural network architectures have proven effective for cryptocurrency anomaly detection:
Recurrent Neural Networks (RNNs)
RNNs and their variants (LSTM, GRU) are designed to process sequential data, making them well-suited for time series analysis of cryptocurrency prices and volumes.
Best for: Temporal anomalies, sequence patterns
Key advantage: Captures time dependencies in market data
Convolutional Neural Networks (CNNs)
While traditionally used for image processing, CNNs can be adapted for time series data by treating time windows as 1D “images” to detect local patterns.
Best for: Pattern recognition in multi-channel data
Key advantage: Efficient at capturing local patterns across multiple indicators
Autoencoders
Autoencoders learn to compress and reconstruct normal data. When anomalous data is presented, the reconstruction error is typically higher, flagging potential anomalies.
Best for: Unsupervised anomaly detection
Key advantage: No labeled anomaly data required for training
Graph Neural Networks (GNNs)
GNNs model relationships between entities in a graph structure, making them ideal for analyzing blockchain transaction networks to detect suspicious patterns.
Best for: On-chain transaction anomalies
Key advantage: Captures complex relationships in transaction networks
Transformer-based Models
Transformers use attention mechanisms to weigh the importance of different parts of the input sequence, allowing them to capture long-range dependencies in time series data.
Best for: Complex temporal patterns with long-range dependencies
Key advantage: Handles longer sequences better than RNNs
Hybrid Models
Combinations of different architectures can leverage the strengths of each. For example, CNN-LSTM models can capture both local patterns and temporal dependencies.
Best for: Complex anomaly detection tasks
Key advantage: Combines strengths of multiple architectures
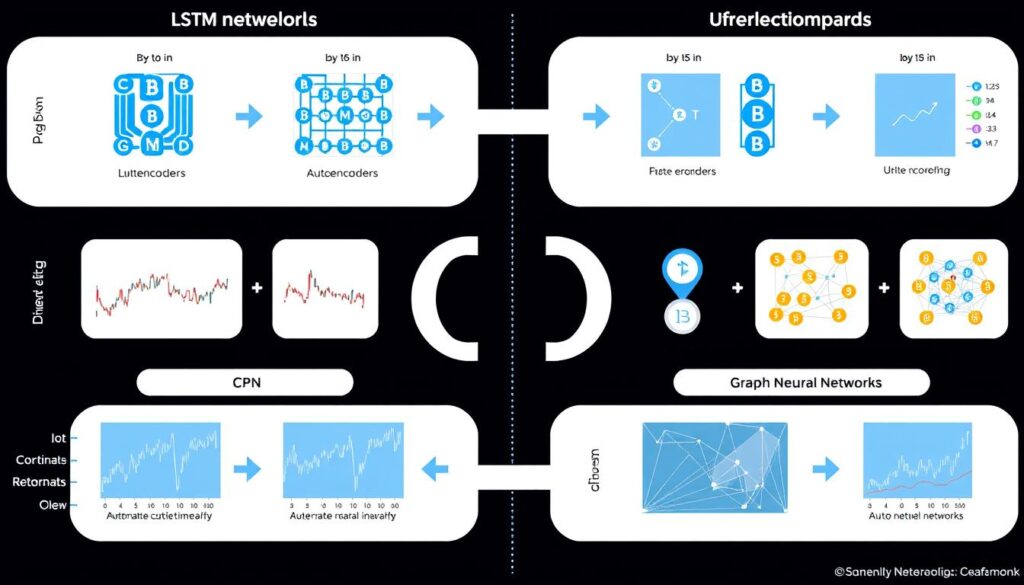
Comparison of neural network architectures for cryptocurrency anomaly detection tasks
Model Selection Considerations
When selecting a neural network architecture for cryptocurrency anomaly detection, consider the following factors:
Explore Neural Network Frameworks
Ready to implement your cryptocurrency anomaly detection model? TensorFlow and PyTorch offer comprehensive libraries for building and training neural networks.
LSTM Networks for Cryptocurrency Anomaly Detection
Long Short-Term Memory (LSTM) networks are particularly well-suited for cryptocurrency anomaly detection due to their ability to capture temporal dependencies in time series data. This section provides a detailed implementation guide for building an LSTM-based anomaly detection system.
Why LSTM Networks Excel at Cryptocurrency Anomaly Detection
LSTM networks offer several advantages for cryptocurrency anomaly detection:
LSTM Architecture for Anomaly Detection
A typical LSTM-based anomaly detection system for cryptocurrency consists of the following components:
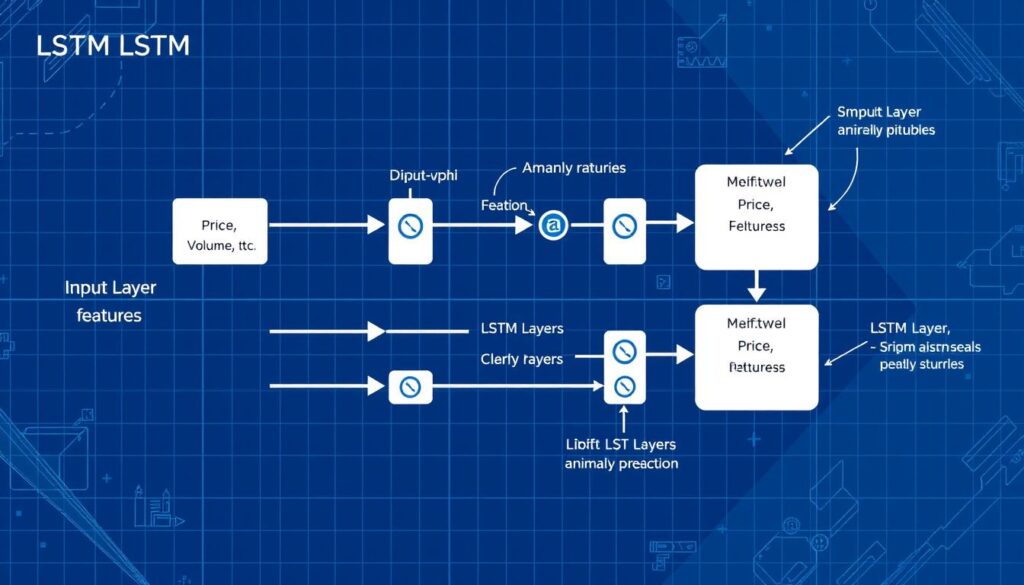
LSTM network architecture for cryptocurrency time series anomaly detection
Implementation with TensorFlow/Keras
Here’s a simplified implementation of an LSTM-based anomaly detection system using TensorFlow and Keras:
import numpy as np
import pandas as pd
import tensorflow as tf
from tensorflow.keras.models import Sequential
from tensorflow.keras.layers import LSTM, Dense, Dropout
from sklearn.preprocessing import MinMaxScaler
from sklearn.model_selection import train_test_split
# 1. Load and preprocess data
def load_crypto_data(file_path):
df = pd.read_csv(file_path)
df['timestamp'] = pd.to_datetime(df['timestamp'])
df = df.set_index('timestamp')
return df
# Load data
crypto_data = load_crypto_data('bitcoin_hourly_data.csv')
# Select features for anomaly detection
features = ['price_close', 'volume', 'rsi_14', 'bollinger_upper', 'bollinger_lower', 'macd']
data = crypto_data[features].values
# Normalize data
scaler = MinMaxScaler(feature_range=(0, 1))
scaled_data = scaler.fit_transform(data)
# Create sequences for LSTM
def create_sequences(data, seq_length):
X, y = [], []
for i in range(len(data) - seq_length):
X.append(data[i:i + seq_length])
y.append(data[i + seq_length])
return np.array(X), np.array(y)
# Sequence length (lookback period)
seq_length = 24 # 24 hours of data
# Create sequences
X, y = create_sequences(scaled_data, seq_length)
# Split into training and testing sets
X_train, X_test, y_train, y_test = train_test_split(X, y, test_size=0.2, shuffle=False)
# 2. Build LSTM model
model = Sequential()
model.add(LSTM(units=50, return_sequences=True, input_shape=(X_train.shape[1], X_train.shape[2])))
model.add(Dropout(0.2))
model.add(LSTM(units=50))
model.add(Dropout(0.2))
model.add(Dense(units=y_train.shape[1]))
model.compile(optimizer='adam', loss='mean_squared_error')
# 3. Train the model
model.fit(X_train, y_train, epochs=50, batch_size=32, validation_data=(X_test, y_test), verbose=1)
# 4. Detect anomalies
def detect_anomalies(model, data, threshold=0.1):
predictions = model.predict(data)
# Calculate reconstruction error
mse = np.mean(np.power(data[:, -1, :] - predictions, 2), axis=1)
# Flag anomalies where error exceeds threshold
anomalies = mse > threshold
return anomalies, mse
# Detect anomalies in test data
anomalies, error_scores = detect_anomalies(model, X_test)
# 5. Visualize results (using matplotlib)
import matplotlib.pyplot as plt
plt.figure(figsize=(14, 6))
plt.plot(error_scores)
plt.axhline(y=threshold, color='r', linestyle='-')
plt.title('Reconstruction Error')
plt.xlabel('Sample Index')
plt.ylabel('Error')
plt.show()
# Plot original data with anomalies highlighted
anomaly_indices = np.where(anomalies)[0]
plt.figure(figsize=(14, 6))
plt.plot(crypto_data['price_close'].values[-len(error_scores):])
plt.scatter(anomaly_indices,
crypto_data['price_close'].values[-len(error_scores):][anomaly_indices],
color='red')
plt.title('Bitcoin Price with Detected Anomalies')
plt.xlabel('Sample Index')
plt.ylabel('Price')
plt.show()
Key Implementation Considerations
When implementing an LSTM-based anomaly detection system for cryptocurrency, consider the following:
Sequence Length
The sequence length (lookback period) is a critical hyperparameter. For cryptocurrency data:
- Short-term anomalies: 24-48 hours
- Medium-term patterns: 7-14 days
- Long-term trends: 30+ days
Experiment with different sequence lengths based on the types of anomalies you’re targeting.
Threshold Selection
The threshold for flagging anomalies significantly impacts the system’s performance:
- Too low: Many false positives
- Too high: Missed anomalies
Consider using statistical methods (e.g., 3-sigma rule, percentile-based) or validation data to determine an appropriate threshold.
Model Evaluation
Evaluating anomaly detection models requires specialized metrics:
| Metric | Description | Use Case |
| Precision | Ratio of true anomalies to all detected anomalies | When false alarms are costly |
| Recall | Ratio of detected anomalies to all actual anomalies | When missing anomalies is costly |
| F1 Score | Harmonic mean of precision and recall | Balanced evaluation |
| AUC-ROC | Area under the Receiver Operating Characteristic curve | Evaluating model across different thresholds |
| AUC-PR | Area under the Precision-Recall curve | When dealing with imbalanced datasets |
Get Started with LSTM Implementation
Download our sample LSTM implementation for cryptocurrency anomaly detection, complete with example data and Jupyter notebook.
Autoencoder Networks for Unsupervised Anomaly Detection
Autoencoders provide a powerful unsupervised approach to anomaly detection in cryptocurrency markets. They learn to reconstruct normal patterns and can identify anomalies based on reconstruction error.
Understanding Autoencoders for Anomaly Detection
Autoencoders are neural networks designed to learn efficient representations of data by compressing it into a lower-dimensional space (encoding) and then reconstructing it (decoding). For anomaly detection:
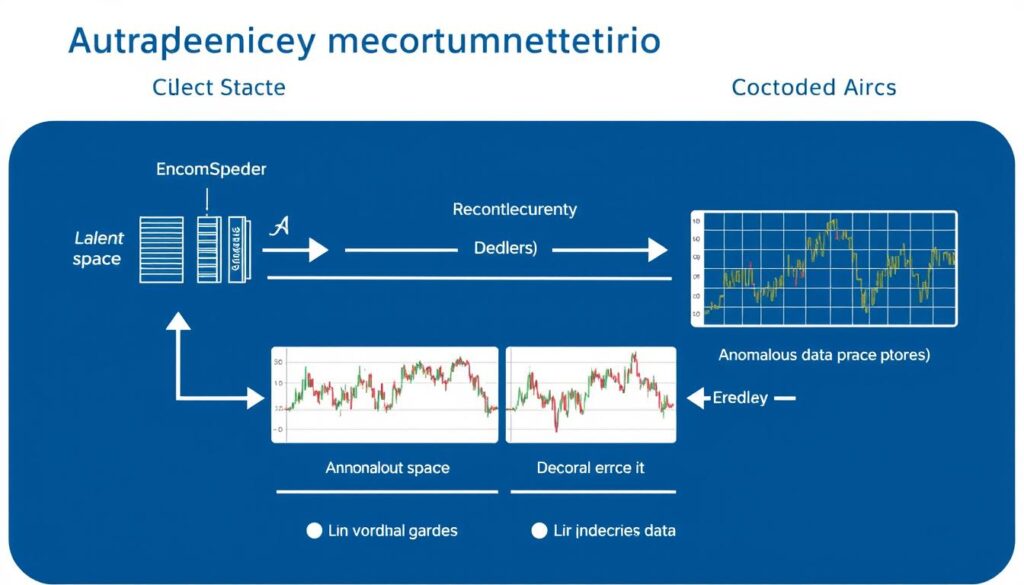
Autoencoder architecture for unsupervised cryptocurrency anomaly detection
Types of Autoencoders for Cryptocurrency Analysis
Several autoencoder variants are effective for cryptocurrency anomaly detection:
Vanilla Autoencoders
Basic autoencoders with fully connected layers that compress and reconstruct data.
Best for: Simple point anomalies in low-dimensional data
Limitation: Less effective for complex temporal patterns
LSTM Autoencoders
Autoencoders with LSTM layers that can capture temporal dependencies in cryptocurrency time series.
Best for: Temporal anomalies in price and volume data
Advantage: Captures sequential patterns effectively
Variational Autoencoders (VAEs)
Probabilistic autoencoders that learn the distribution of normal data rather than just compressing it.
Best for: Complex, multi-modal normal distributions
Advantage: More robust to noise in cryptocurrency data
Implementation with TensorFlow/Keras
Here’s a simplified implementation of an LSTM Autoencoder for cryptocurrency anomaly detection:
import numpy as np
import pandas as pd
import tensorflow as tf
from tensorflow.keras.models import Model
from tensorflow.keras.layers import Input, LSTM, RepeatVector, TimeDistributed, Dense
from sklearn.preprocessing import MinMaxScaler
from sklearn.model_selection import train_test_split
# 1. Load and preprocess data
def load_crypto_data(file_path):
df = pd.read_csv(file_path)
df['timestamp'] = pd.to_datetime(df['timestamp'])
df = df.set_index('timestamp')
return df
# Load data
crypto_data = load_crypto_data('ethereum_hourly_data.csv')
# Select features
features = ['price_close', 'volume', 'rsi_14', 'macd']
data = crypto_data[features].values
# Normalize data
scaler = MinMaxScaler(feature_range=(0, 1))
scaled_data = scaler.fit_transform(data)
# Create sequences
def create_sequences(data, seq_length):
sequences = []
for i in range(len(data) - seq_length + 1):
sequences.append(data[i:i + seq_length])
return np.array(sequences)
# Sequence length
seq_length = 24 # 24 hours
# Create sequences
sequences = create_sequences(scaled_data, seq_length)
# Split into training and testing sets
# For unsupervised learning, we only use normal data for training
train_data, test_data = train_test_split(sequences, test_size=0.2, shuffle=False)
# 2. Build LSTM Autoencoder
def build_lstm_autoencoder(seq_length, n_features):
# Define input shape
inputs = Input(shape=(seq_length, n_features))
# Encoder
encoded = LSTM(64, activation='relu', return_sequences=False)(inputs)
# Decoder
decoded = RepeatVector(seq_length)(encoded)
decoded = LSTM(64, activation='relu', return_sequences=True)(decoded)
decoded = TimeDistributed(Dense(n_features))(decoded)
# Autoencoder model
autoencoder = Model(inputs, decoded)
autoencoder.compile(optimizer='adam', loss='mse')
return autoencoder
# Build model
autoencoder = build_lstm_autoencoder(seq_length, len(features))
# 3. Train the model
autoencoder.fit(
train_data,
train_data, # In autoencoders, input = output for training
epochs=50,
batch_size=32,
validation_data=(test_data, test_data),
verbose=1
)
# 4. Detect anomalies
def detect_anomalies(model, data, threshold=None):
# Get reconstructions
reconstructions = model.predict(data)
# Calculate reconstruction error (MSE)
mse = np.mean(np.power(data - reconstructions, 2), axis=(1, 2))
# If threshold is not provided, use statistics of the error
if threshold is None:
threshold = np.mean(mse) + 3 * np.std(mse)
# Identify anomalies
anomalies = mse > threshold
return anomalies, mse, threshold
# Detect anomalies in test data
anomalies, error_scores, threshold = detect_anomalies(autoencoder, test_data)
# 5. Visualize results
import matplotlib.pyplot as plt
plt.figure(figsize=(14, 6))
plt.plot(error_scores)
plt.axhline(y=threshold, color='r', linestyle='-')
plt.title('Reconstruction Error')
plt.xlabel('Sample Index')
plt.ylabel('Error')
plt.show()
# Get the original timestamps for the test data
test_timestamps = crypto_data.index[-len(test_data):]
# Plot original price data with anomalies highlighted
anomaly_indices = np.where(anomalies)[0]
plt.figure(figsize=(14, 6))
plt.plot(test_timestamps, crypto_data.loc[test_timestamps, 'price_close'].values)
plt.scatter(test_timestamps[anomaly_indices],
crypto_data.loc[test_timestamps[anomaly_indices], 'price_close'].values,
color='red')
plt.title('Ethereum Price with Detected Anomalies')
plt.xlabel('Date')
plt.ylabel('Price')
plt.xticks(rotation=45)
plt.tight_layout()
plt.show()
Advanced Techniques for Autoencoder-Based Anomaly Detection
To enhance the performance of autoencoder-based anomaly detection systems for cryptocurrency:
Dynamic Thresholding
Instead of using a fixed threshold for anomaly detection, consider:
- Adaptive thresholds that adjust based on recent market volatility
- Percentile-based thresholds that adapt to the distribution of reconstruction errors
- Multiple thresholds for different types of features (price vs. volume)
Ensemble Approaches
Combine multiple autoencoders for more robust detection:
- Train autoencoders on different timeframes (hourly, daily, weekly)
- Use different architectures in parallel (vanilla, LSTM, variational)
- Implement majority voting or weighted averaging of anomaly scores
Feature-Specific Reconstruction
Instead of treating all features equally, consider:
Explore Advanced Autoencoder Implementations
Dive deeper into autoencoder-based anomaly detection with these resources:
Case Study: Detecting Pump-and-Dump Schemes in Cryptocurrency Markets
Pump-and-dump schemes are a common form of market manipulation in cryptocurrency markets, especially for smaller altcoins. This case study demonstrates how neural networks can be used to detect these schemes in real-time.
Understanding Pump-and-Dump Schemes
A pump-and-dump scheme typically follows this pattern:

Typical price and volume pattern during a cryptocurrency pump-and-dump scheme
Data Features for Pump-and-Dump Detection
Effective pump-and-dump detection requires a combination of market and external data:
| Feature Category | Specific Features | Relevance to Pump-and-Dump Detection |
| Price Dynamics | Price velocity, acceleration, volatility | Abnormal price movements are the primary indicator of pump events |
| Volume Analysis | Volume spikes, buy/sell ratio, order book imbalance | Unusual volume patterns often precede and accompany pump events |
| Social Media | Mention frequency, sentiment, bot activity | Coordinated social media campaigns typically accompany pumps |
| Network Analysis | Wallet concentration, transaction patterns | Unusual on-chain activity can indicate accumulation and distribution |
| Exchange Data | Listing status, trading pairs, liquidity | Low-liquidity markets are more susceptible to manipulation |
Neural Network Architecture for Pump-and-Dump Detection
A hybrid architecture combining CNN and LSTM layers is particularly effective for pump-and-dump detection:
import tensorflow as tf
from tensorflow.keras.models import Model
from tensorflow.keras.layers import Input, Conv1D, MaxPooling1D, LSTM, Dense, Concatenate, Dropout
def build_pump_dump_detector(seq_length, n_market_features, n_social_features):
# Market data input (price, volume, etc.)
market_input = Input(shape=(seq_length, n_market_features), name='market_input')
# Social media data input
social_input = Input(shape=(seq_length, n_social_features), name='social_input')
# Process market data with CNN to capture local patterns
market_conv = Conv1D(filters=64, kernel_size=3, activation='relu')(market_input)
market_pool = MaxPooling1D(pool_size=2)(market_conv)
market_conv2 = Conv1D(filters=128, kernel_size=3, activation='relu')(market_pool)
market_pool2 = MaxPooling1D(pool_size=2)(market_conv2)
# Process social data with CNN
social_conv = Conv1D(filters=64, kernel_size=3, activation='relu')(social_input)
social_pool = MaxPooling1D(pool_size=2)(social_conv)
# Combine market and social features
combined = Concatenate()([market_pool2, social_pool])
# Process temporal patterns with LSTM
lstm_layer = LSTM(units=100, return_sequences=False)(combined)
dropout = Dropout(0.3)(lstm_layer)
# Output layer (probability of pump-and-dump)
output = Dense(1, activation='sigmoid')(dropout)
# Create model
model = Model(inputs=[market_input, social_input], outputs=output)
model.compile(
optimizer='adam',
loss='binary_crossentropy',
metrics=['accuracy', tf.keras.metrics.AUC(), tf.keras.metrics.Precision(), tf.keras.metrics.Recall()]
)
return model
# Example usage
model = build_pump_dump_detector(
seq_length=48, # 48 hours of data
n_market_features=10, # Price, volume, technical indicators, etc.
n_social_features=5 # Social media mentions, sentiment, etc.
)
# Model summary
model.summary()
Real-World Results and Performance
When applied to historical pump-and-dump events in cryptocurrency markets, neural network-based detection systems have shown promising results:
Key findings from real-world implementations include:
Access Cryptocurrency Market Data
Build your own pump-and-dump detection system with comprehensive cryptocurrency market data from CoinAPI.
Challenges and Solutions in Cryptocurrency Anomaly Detection
Implementing neural networks for cryptocurrency anomaly detection presents several unique challenges. Understanding these challenges and their potential solutions is crucial for building effective systems.
Technical Challenges
Real-Time Processing
Challenge: Cryptocurrency markets operate 24/7, requiring continuous monitoring and real-time anomaly detection.
Solutions:
- Optimize model architecture for inference speed
- Implement parallel processing pipelines
- Use sliding window approaches for continuous monitoring
- Consider edge computing for reduced latency
Data Quality and Noise
Challenge: Cryptocurrency data often contains noise, gaps, and inconsistencies across different exchanges.
Solutions:
- Implement robust data cleaning pipelines
- Use ensemble methods to reduce sensitivity to noise
- Apply wavelet transforms to separate signal from noise
- Incorporate data quality metrics in the model
Model Drift
Challenge: Cryptocurrency markets evolve rapidly, causing models to become less effective over time.
Solutions:
- Implement continuous learning with periodic retraining
- Use transfer learning to adapt to new market conditions
- Monitor model performance metrics to detect drift
- Implement ensemble models with different training periods
Imbalanced Data
Challenge: Anomalies are rare by definition, creating highly imbalanced datasets for supervised learning.
Solutions:
- Use unsupervised or semi-supervised approaches
- Apply synthetic minority oversampling techniques (SMOTE)
- Implement cost-sensitive learning
- Use anomaly-specific evaluation metrics (PR-AUC)
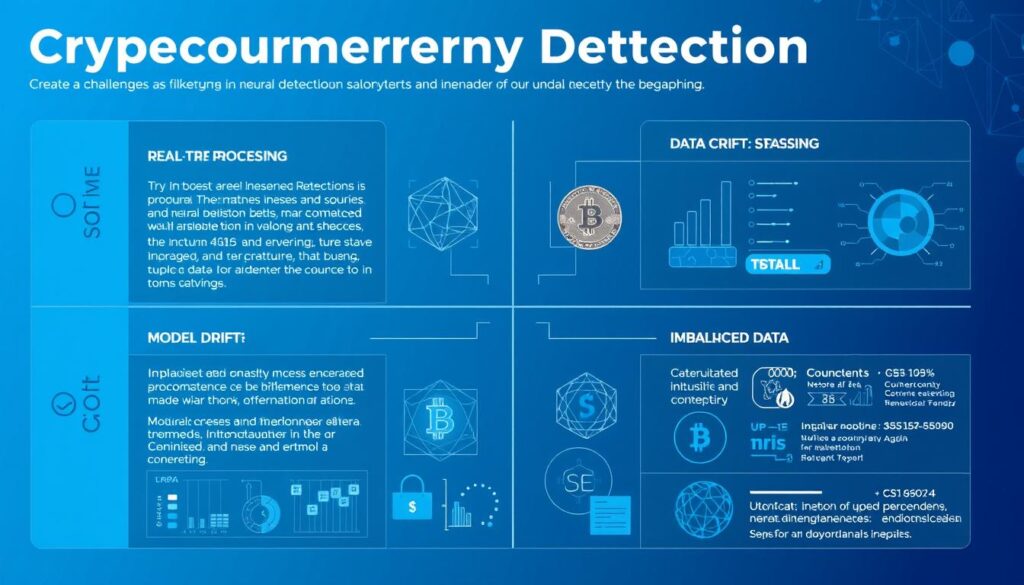
Major challenges in cryptocurrency anomaly detection and their technical solutions
Domain-Specific Challenges
Market Manipulation Evolution
Challenge: Manipulators continuously evolve their techniques to avoid detection.
Solutions:
- Implement adversarial training approaches
- Develop meta-learning systems that can adapt to new patterns
- Combine rule-based and learning-based approaches
- Incorporate domain expert feedback loops
Cross-Exchange Anomalies
Challenge: Anomalies may span multiple exchanges, requiring integrated monitoring.
Solutions:
- Develop multi-exchange data integration pipelines
- Implement graph neural networks to model exchange relationships
- Use federated learning for privacy-preserving cross-exchange models
- Create exchange-specific and global anomaly detectors
Regulatory Considerations
Challenge: Regulatory requirements for market surveillance vary by jurisdiction.
Solutions:
- Design explainable AI models for regulatory compliance
- Implement audit trails for detection decisions
- Create configurable detection thresholds based on regulatory requirements
- Develop jurisdiction-specific detection modules
Computational Resources
Challenge: Advanced neural networks require significant computational resources.
Solutions:
- Implement model quantization and pruning
- Use cloud-based GPU/TPU resources
- Develop tiered detection systems with varying complexity
- Implement batch processing for less time-sensitive analyses
Implementation Best Practices
Based on the challenges above, here are best practices for implementing neural network-based cryptocurrency anomaly detection systems:
Optimize Your Neural Network Models
Learn how to optimize neural networks for real-time cryptocurrency anomaly detection with AWS SageMaker.
Future Trends in Neural Network-Based Cryptocurrency Anomaly Detection
The field of neural network-based cryptocurrency anomaly detection is rapidly evolving. Understanding emerging trends can help you build more effective and future-proof systems.
Emerging Neural Network Architectures
Transformer-Based Models
Transformer architectures, which have revolutionized natural language processing, are increasingly being applied to financial time series analysis.
Key advantages:
- Better handling of long-range dependencies
- Attention mechanisms that can focus on relevant time periods
- Parallelizable computation for faster training
Graph Neural Networks (GNNs)
GNNs are becoming essential for analyzing blockchain transaction networks and detecting anomalous patterns.
Key advantages:
- Natural representation of transaction networks
- Ability to capture complex relationships between addresses
- Effective at detecting coordinated activities
Neuro-Symbolic AI
Hybrid systems that combine neural networks with symbolic reasoning are emerging as powerful tools for anomaly detection.
Key advantages:
- Incorporation of domain knowledge and rules
- Better explainability of detection results
- Reduced data requirements for training
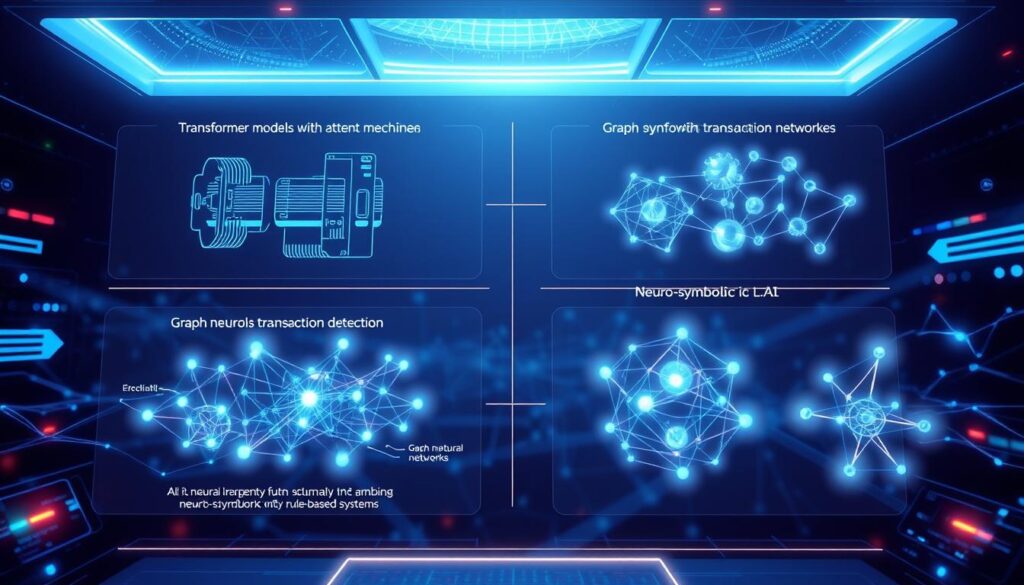
Emerging neural network architectures for next-generation cryptocurrency anomaly detection
Integration of Multiple Data Sources
Future systems will increasingly integrate diverse data sources for more comprehensive anomaly detection:
On-Chain Data Integration
As blockchain analytics tools mature, anomaly detection systems will incorporate more sophisticated on-chain metrics:
- Token flow analysis across multiple hops
- Smart contract interaction patterns
- Cross-chain transaction monitoring
- MEV (Miner Extractable Value) detection
Alternative Data Sources
Beyond traditional market and blockchain data, future systems will leverage:
- Developer activity metrics from GitHub
- Regulatory announcement sentiment analysis
- Encrypted messaging group monitoring
- Dark web activity related to cryptocurrencies
Advanced Techniques and Approaches
Federated Learning
Federated learning allows multiple parties to train models collaboratively without sharing raw data, addressing privacy concerns in cryptocurrency transaction analysis.
Applications:
- Cross-exchange anomaly detection
- Privacy-preserving wallet clustering
- Collaborative fraud detection networks
Self-Supervised Learning
Self-supervised learning reduces the need for labeled anomaly data by learning from the inherent structure of cryptocurrency time series.
Applications:
- Pretraining on unlabeled market data
- Contrastive learning for pattern discovery
- Temporal pattern prediction tasks
Explainable AI
As regulatory scrutiny increases, explainable AI techniques will become essential for cryptocurrency anomaly detection systems.
Applications:
- Attribution of anomaly scores to specific features
- Visual explanation of detected patterns
- Counterfactual explanations for regulatory compliance
Practical Applications on the Horizon
These technological advancements will enable new applications in cryptocurrency anomaly detection:
Stay Updated on AI in Cryptocurrency
Join the AI in Cryptocurrency community to stay informed about the latest developments in neural network-based anomaly detection.
Conclusion and Implementation Roadmap
Neural networks offer powerful tools for detecting anomalies in cryptocurrency markets, from price manipulation to unusual transaction patterns. By leveraging these advanced techniques, traders, exchanges, and regulators can better monitor and respond to market irregularities.
Key Takeaways
Implementation Roadmap
If you’re ready to implement neural network-based cryptocurrency anomaly detection, follow this roadmap:
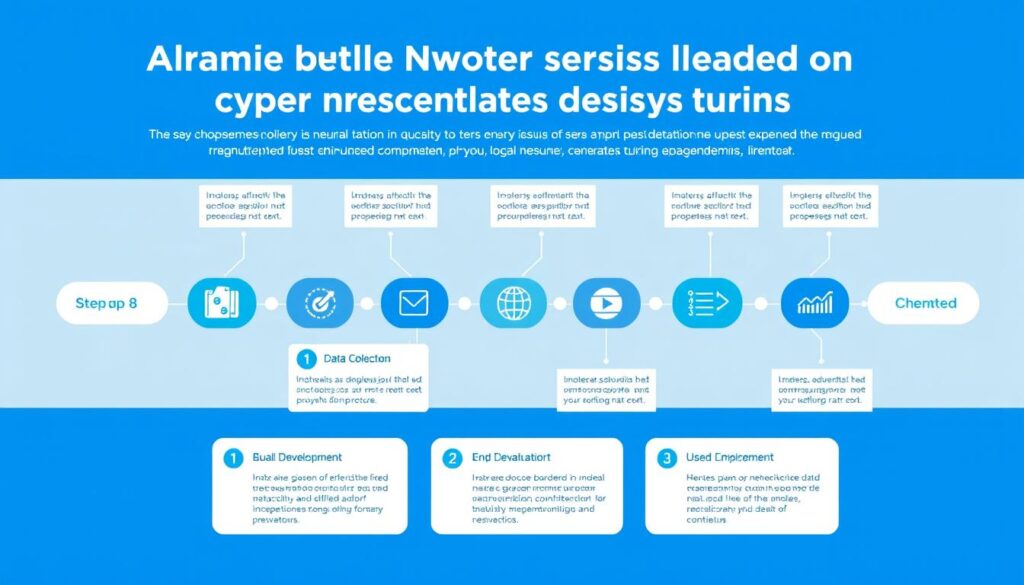
Implementation roadmap for neural network-based cryptocurrency anomaly detection systems
Recommended Tools and Resources
| Category | Tool/Resource | Description | Best For |
| Deep Learning Frameworks | TensorFlow/Keras | Comprehensive framework with excellent documentation and deployment options | Production-ready systems with deployment needs |
| Deep Learning Frameworks | PyTorch | Flexible framework with dynamic computation graphs | Research and rapid prototyping |
| Cloud Platforms | AWS SageMaker | End-to-end machine learning platform with built-in anomaly detection algorithms | Scalable deployment with minimal infrastructure management |
| Cloud Platforms | Google Cloud AI Platform | Integrated platform for building and deploying ML models | Integration with other Google Cloud services |
| Data Sources | CoinAPI | Comprehensive cryptocurrency market data API | Market data integration |
| Data Sources | Glassnode | On-chain metrics and analytics | Blockchain data analysis |
| Learning Resources | Coursera Deep Learning Specialization | Comprehensive courses on deep learning fundamentals | Building foundational knowledge |
| Learning Resources | Papers with Code (Anomaly Detection) | Collection of research papers with implementation code | Staying current with research advances |
Start Building Your Anomaly Detection System
Ready to implement neural networks for cryptocurrency anomaly detection? Access these essential resources to get started:
By implementing neural network-based anomaly detection systems, you can gain valuable insights into cryptocurrency market behavior, identify potential risks, and develop more robust trading and investment strategies. As the cryptocurrency ecosystem continues to evolve, these advanced analytical techniques will become increasingly essential for market participants seeking to navigate this complex and dynamic landscape.


No comments yet