Imagine proving you know a secret without whispering a single word. This powerful idea forms the core of a groundbreaking cryptographic method. It allows secure verification while keeping sensitive details completely hidden.
Researchers Shafi Goldwasser and Silvio Micali first introduced this concept in a landmark 1985 MIT paper. Their work laid the foundation for a new way to handle digital trust. The World Economic Forum later recognized its immense potential, naming it a key privacy-enhancing technology in 2019.
This method solves a critical challenge in modern digital systems. How can we maintain transparency for trust while fiercely protecting user privacy? It strikes a perfect balance, confirming actions are valid without exposing the underlying data.
Today, this innovation is transforming how we secure information across decentralized networks. Its ability to validate transactions confidentially makes it invaluable for sectors like finance and healthcare. For a deeper exploration of how zero-knowledge proofs function, our guide provides clear explanations.
Key Takeaways
- Zero-knowledge proofs enable verification without revealing the actual information.
- The concept originated from academic research in the 1980s.
- This technology balances the need for transparency with strong privacy protection.
- Major institutions like the World Economic Forum have recognized its importance.
- It is particularly valuable for applications in finance, healthcare, and other sensitive fields.
- The core idea allows one party to prove knowledge to another without sharing data.
Introduction to Zero-Knowledge Proof Blockchain Privacy
The digital age presents a unique challenge: how to build trust without compromising sensitive details. Distributed ledger systems offer unprecedented openness but create significant confidentiality concerns for users.
Overview of the Concept and Importance
Public networks maintain complete transaction histories visible to all participants. This permanent record links sender and receiver addresses, creating traceable financial footprints.
While these systems provide pseudonymity rather than true anonymity, associating an address with real identity exposes entire transaction histories. This creates substantial risks for handling medical records, financial details, and business operations.
The technology represents a crucial innovation for balancing verification needs with confidentiality requirements. It allows confirmation of valid actions while keeping underlying information completely hidden.
Emergence in Modern Blockchain Applications
Growing demands for confidentiality in financial services, healthcare, and supply chain management drive adoption. Enterprises seek solutions that comply with regulations like GDPR and HIPAA while leveraging public network benefits.
Modern implementations enable verification of transactions and computations without disclosing source material. This opens new possibilities for Web3 development and enterprise solutions.
The approach addresses fundamental tensions between accountability and protection of personal information. Institutions can maintain regulatory compliance while participating in transparent ecosystems.
What is Zero Knowledge Proof Blockchain Privacy?
At its heart, this cryptographic method involves two distinct roles: a prover and a verifier. The prover holds specific information and aims to demonstrate its validity. The verifier’s job is to confirm this claim without learning the secret data itself.

The entire process is built around a single, crucial statement. The prover convinces the verifier that this statement is true. This happens without revealing any details beyond the fact of its truth.
This allows for secure validation on open networks. Sensitive details remain completely confidential. You can learn more about the mechanics of this powerful cryptographic protocol in our dedicated guide.
Essentially, it’s a way to share proof of knowledge, not the knowledge itself. This solves a major challenge for systems that require both transparency and strong confidentiality.
Fundamentals of Zero-Knowledge Proofs
The strength of modern cryptographic methods stems from a trio of essential guarantees. These properties ensure the entire system functions reliably and securely.
Core Principles: Completeness, Soundness, and Zero-Knowledge
Every valid proof must satisfy three fundamental properties. Completeness means an honest prover can always convince an honest verifier of a true statement.
Soundness protects against deception. A dishonest prover cannot trick the verifier into accepting a false claim.
The final property ensures the verifier learns nothing beyond the statement’s validity. This protects the underlying information completely.
Historical Background and Evolution in Cryptography
This revolutionary concept emerged from a landmark 1985 MIT paper. Shafi Goldwasser and Silvio Micali introduced “The Knowledge Complexity of Interactive Proof-Systems.”
Early zero-knowledge proofs were interactive, requiring a challenge-response process for each verification. This method involved multiple rounds between the two parties.
Evolution led to non-interactive proofs. A single proof can now be verified by anyone, saving significant time. For a detailed exploration of these proofs, further resources are available.
This way of confirming knowledge without disclosure has become a cornerstone of advanced cryptography.
Implementations and Types of Zero-Knowledge Proofs
Several practical implementations have emerged to apply this verification method. Each offers distinct advantages for different applications.
zk-SNARKs and Their Practical Applications
zk-SNARKs represent an early breakthrough in this field. These succinct non-interactive arguments provide compact verification.
The technology requires a trusted setup process. This generates initial parameters using sensitive data that must be securely destroyed.
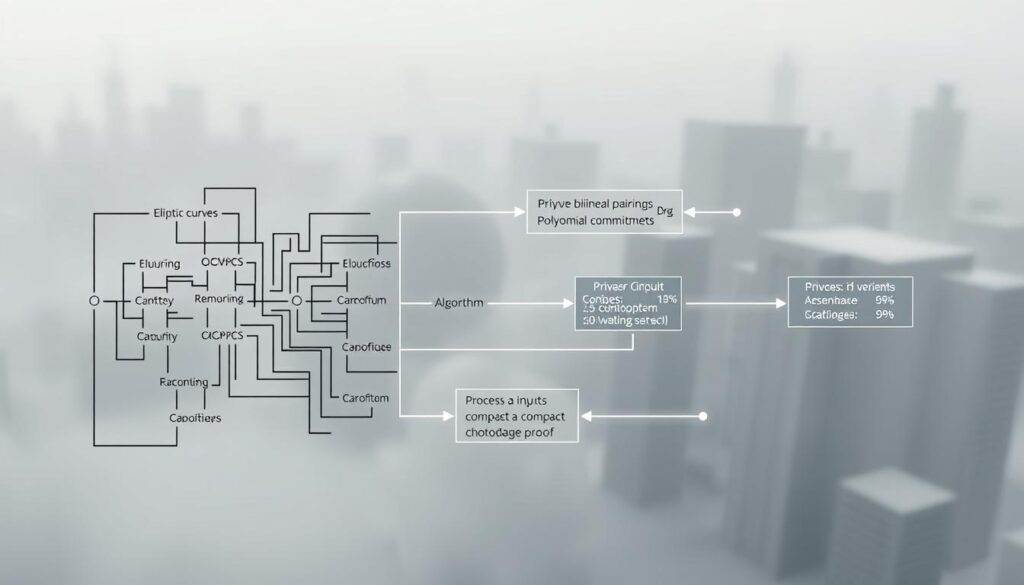
zk-STARKs, PLONK, and Bulletproofs
zk-STARKs eliminate the need for trusted setup. They offer scalable transparent verification with quantum resistance.
PLONK uses a universal trusted setup applicable to various programs. Bulletproofs enable private transactions without setup requirements.
| Implementation | Trusted Setup | Proof Size | Key Feature |
|---|---|---|---|
| zk-SNARKs | Required | Small | Fast verification |
| zk-STARKs | Not required | Larger | Quantum secure |
| PLONK | Universal | Medium | Flexible application |
| Bulletproofs | Not required | Compact | Transaction privacy |
Real-world applications include Zcash using zk-SNARKs and StarkNet leveraging zk-STARKs. These protocols demonstrate practical use across different platforms.
Blockchain and Privacy: Addressing Limitations
A fundamental tension exists between the open nature of decentralized networks and the need for confidentiality. The features that make distributed ledgers secure—transparency and immutability—also create significant hurdles for handling sensitive data.
Traditional architectures are not well-suited for financial records, medical history, or proprietary business information. They offer pseudonymity, not true anonymity, which falls short of modern privacy standards.
Challenges with Transactional Linkability
Every action on a public ledger is permanently recorded and interconnected. This creates a traceable network of transactions.
Analyzing patterns can potentially reveal the identities behind public addresses. Once an address is linked to a person, their entire financial history becomes visible.
This level of exposure poses risks for individuals and enterprises alike. Protecting personal information under such conditions is a major challenge.
Smart Contract Transparency Versus Data Privacy
Self-executing contracts have their code stored openly on the network. This transparency is essential for trust but can expose sensitive business logic.
Companies may hesitate to use smart contracts for proprietary operations. The need to safeguard trade secrets conflicts with the ledger’s open nature.
This makes traditional systems unviable for confidential commercial information. A new solution is required to bridge this gap effectively.
Use Cases and Benefits of Zero-Knowledge Proofs on the Blockchain
From financial services to identity management, advanced verification protocols are revolutionizing how we handle sensitive information. These practical applications demonstrate significant value across multiple sectors.

Private Transactions and Verifiable Computations
Cryptocurrencies like Zcash employ these methods to conceal transaction details. Amounts, sender, and receiver addresses remain confidential throughout the process.
Verifiable computations enable layer 2 scaling solutions. zk-Rollups process transactions off-chain while submitting validity proofs. This approach enhances speed and reduces costs significantly.
DECO, a privacy-preserving oracle protocol, guarantees data remains secure during delivery. It maintains the TLS chain of custody from various sources.
Decentralized Identity and Authentication
Identity management systems leverage these techniques for secure validation. Users can prove citizenship or age without disclosing passport details or birthdates.
The W3C’s verifiable credentials standard incorporates selective disclosure. Individuals demonstrate specific attributes like university degrees while protecting personal information.
Financial institutions use range proofs for mortgage applications. Applicants show income falls within required ranges without revealing exact amounts. This protects sensitive financial data effectively.
Overcoming Challenges and Future Prospects
The evolution of communication infrastructure has transformed the practical implementation of confidential verification methods. Earlier obstacles like high data volume and slow processing speeds are becoming manageable.
Modern hardware advancements effectively eliminate historical bottlenecks. Faster networks and secure memory areas in devices make these systems more accessible.
Scalability, Security, and Technological Advances
Non-interactive verification requires only a single message between parties. This significantly reduces computational overhead compared to multiple-round approaches.
Security enhancements include quantum-resistant systems like zk-STARKs. These protect against future threats from advanced computing technology.
The method brings trustworthiness to Web3 privacy infrastructure. Major institutions recognize its value for financial services and other sensitive applications.
Future prospects span healthcare, finance, and enterprise operations. Institutions can leverage public network benefits without surrendering control of proprietary datasets.
This solution enables previously inaccessible use cases across sectors. As applications evolve, the technology will drive the next stage of digital revolution.
Conclusion
The future of secure digital interaction rests on a powerful cryptographic breakthrough. This innovation masterfully resolves the core tension between system openness and individual confidentiality.
Enterprises gain a significant advantage. They can now leverage the reliability of public networks while keeping internal datasets completely private. This opens doors for sensitive applications in finance and healthcare.
The method’s strength lies in its elegant process. One party (the prover) convinces another (the verifier) of a statement’s truth. This happens without revealing the underlying information.
Guarantees of completeness, soundness, and zero-knowledge ensure integrity. These properties protect sensitive data across various use cases.
From theoretical concept to practical technology, these proofs represent a game-changer. They are essential for the next stage of digital evolution, blending transparency with the security modern users demand.
FAQ
How do zero-knowledge proofs enhance security without revealing personal information?
These protocols allow a prover to convince a verifier that a statement is true without disclosing any underlying data. This process strengthens security by validating information like identity or transaction value while keeping the actual details confidential.
What is the difference between zk-SNARKs and zk-STARKs?
zk-SNARKs, or succinct non-interactive arguments of knowledge, require a trusted setup but produce very small proof sizes. zk-STARKs offer scalable transparent arguments without a trusted setup and are generally faster, but the proof size is larger.
Can this technology be used for authentication on a public ledger?
Absolutely. One powerful application is for decentralized identity. A person can prove they are of legal age or have a valid credential without showing their driver’s license or passport, enhancing privacy in authentication processes.
Do these proofs make blockchain transactions completely private?
They significantly increase privacy by breaking transactional linkability. While the transaction is recorded on the ledger, the details are hidden, allowing for verifiable computations without exposing sensitive information.
What are the main challenges with current zero-knowledge proof protocols?
Key challenges include achieving scalability for mass adoption, managing computational complexity, and for some systems like zk-SNARKs, the initial requirement for a trusted setup. Technological advances are continuously addressing these hurdles.


No comments yet