Zero-knowledge proofs (ZKPs) represent one of the most powerful cryptographic innovations in blockchain technology. They allow one party to prove to another that a statement is true without revealing any information beyond the validity of the statement itself. For blockchain developers and architects, ZKPs offer a dual promise: enhanced privacy and improved scalability—two of the most pressing challenges in blockchain adoption. This technical guide will walk you through implementing ZKPs in blockchain applications, with practical code examples and frameworks to get you started.
Understanding Zero-Knowledge Proofs
Figure 1: The fundamental concept of zero-knowledge proofs – proving knowledge without revealing it
A zero-knowledge proof is a cryptographic method that enables one party (the prover) to convince another party (the verifier) that a statement is true without revealing any information apart from the fact that the statement is true. First introduced in a 1985 paper titled “The knowledge complexity of interactive proof systems” by Shafi Goldwasser, Silvio Micali, and Charles Rackoff, ZKPs have evolved from theoretical constructs to practical implementations.
For a protocol to qualify as a zero-knowledge proof, it must satisfy three essential properties:
- Completeness: If the statement is true and both parties follow the protocol, the verifier will be convinced of this fact.
- Soundness: If the statement is false, no cheating prover can convince an honest verifier that it is true, except with negligible probability.
- Zero-knowledge: If the statement is true, the verifier learns nothing other than the fact that the statement is true.
Types of Zero-Knowledge Proofs
There are several types of zero-knowledge proofs, but in the blockchain context, two implementations have gained significant traction:
| Feature | ZK-SNARKs | ZK-STARKs |
| Full Name | Zero-Knowledge Succinct Non-Interactive Argument of Knowledge | Zero-Knowledge Scalable Transparent Argument of Knowledge |
| Trusted Setup | Required | Not required |
| Proof Size | Smaller (~100-200 bytes) | Larger (~10-100 KB) |
| Verification Time | Faster for smaller proofs | Faster for larger computations |
| Cryptographic Assumptions | Elliptic curve cryptography | Hash functions (collision-resistant) |
| Quantum Resistance | Vulnerable | Resistant |
| Notable Implementations | Zcash, Loopring, zkSync | StarkWare, Immutable X |
The Dual Benefits: Privacy and Scalability
Enhanced Privacy
Zero-knowledge proofs enable blockchain applications to verify transactions without revealing sensitive information. This privacy-preserving capability is crucial for:
- Private Transactions: Allowing users to transfer assets without revealing amounts or addresses
- Identity Verification: Proving eligibility or credentials without exposing personal data
- Confidential Business Logic: Executing smart contracts with proprietary algorithms while maintaining verifiability
- Regulatory Compliance: Meeting KYC/AML requirements while preserving user privacy
Improved Scalability
Beyond privacy, ZKPs offer significant scalability benefits through:
- Computation Compression: Representing complex computations as succinct proofs
- ZK-Rollups: Batching multiple transactions into a single proof for efficient verification
- Validity Proofs: Ensuring correctness of off-chain computations without re-executing them
- Reduced On-chain Footprint: Minimizing data storage requirements on the main chain
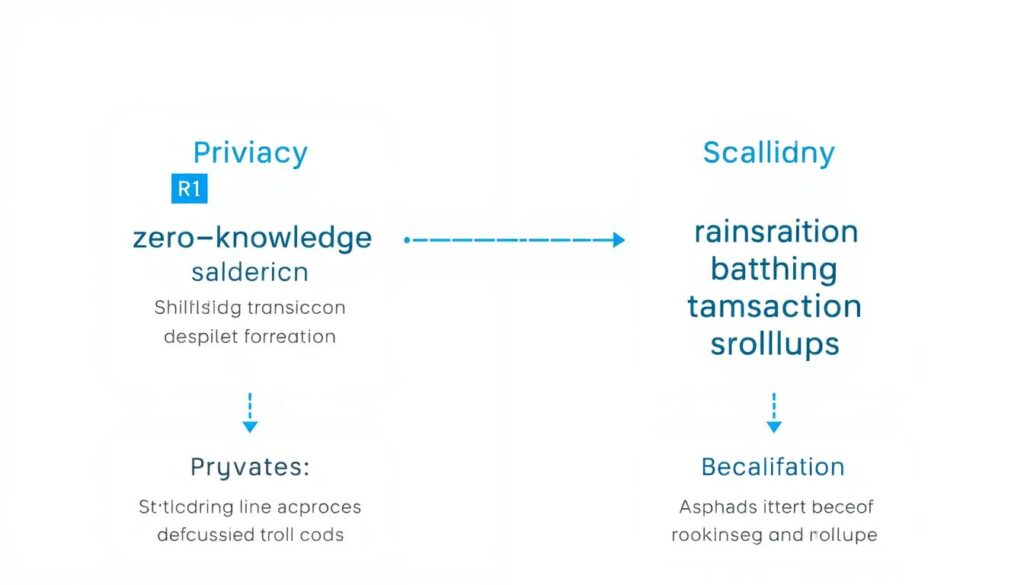
Figure 2: The dual benefits of zero-knowledge proofs in blockchain applications
Implementation Steps for Zero-Knowledge Proofs
Implementing ZKPs in blockchain applications involves several key steps, from defining the statements to be proven to integrating the verification process in smart contracts. Let’s explore the implementation process with practical examples.
Step 1: Define the Statement to be Proven
The first step is to clearly define what you want to prove in zero-knowledge. This could be knowledge of a secret, ownership of assets, or the validity of a computation. The statement must be expressible as a mathematical constraint system.
Figure 3: Converting statements into mathematical constraint systems
Step 2: Implement ZK-SNARKs in Ethereum Smart Contracts
For Ethereum-based applications, implementing ZK-SNARKs involves working with verification contracts. Here’s a simplified example of a ZK-SNARK verifier in Solidity:
// SPDX-License-Identifier: MIT
pragma solidity ^0.8.0;
import "@openzeppelin/contracts/utils/cryptography/ECDSA.sol";
contract ZKSnarkVerifier {
// Verification key components
struct VerifyingKey {
uint256[] alpha;
uint256[] beta;
uint256[] gamma;
uint256[] delta;
uint256[][] IC;
}
VerifyingKey public vk;
constructor(
uint256[] memory _alpha,
uint256[] memory _beta,
uint256[] memory _gamma,
uint256[] memory _delta,
uint256[][] memory _IC
) {
vk.alpha = _alpha;
vk.beta = _beta;
vk.gamma = _gamma;
vk.delta = _delta;
vk.IC = _IC;
}
function verify(
uint256[] memory proof,
uint256[] memory input
) public view returns (bool) {
// Verification logic implementation
// This is a simplified placeholder - actual implementation
// would perform pairing checks and other cryptographic operations
return performVerification(proof, input, vk);
}
function performVerification(
uint256[] memory proof,
uint256[] memory input,
VerifyingKey memory _vk
) internal pure returns (bool) {
// Actual cryptographic verification
// ...
// Simplified for demonstration
return true;
}
}
Ready to Implement ZK-SNARKs?
Get access to complete code examples and libraries for implementing ZK-SNARKs in your Ethereum projects.
Step 3: Implement ZK-STARKs for Scalable Applications
For applications requiring quantum resistance or handling larger proofs, ZK-STARKs offer advantages. Here’s a simplified example using the StarkWare library in a Rust implementation:
use stark_crypto::stark::{Prover, Verifier};
use stark_crypto::field::FieldElement;
fn main() {
// Define the computation to be proven
let computation = |input: &[FieldElement]| -> Vec {
// Example: Prove we know the preimage of a hash
// ...
vec![/* output elements */]
};
// Generate a proof
let input = vec![/* input elements */];
let prover = Prover::new();
let proof = prover.prove(&computation, &input);
// Verify the proof
let verifier = Verifier::new();
let is_valid = verifier.verify(&proof, &computation);
println!("Proof verification result: {}", is_valid);
}
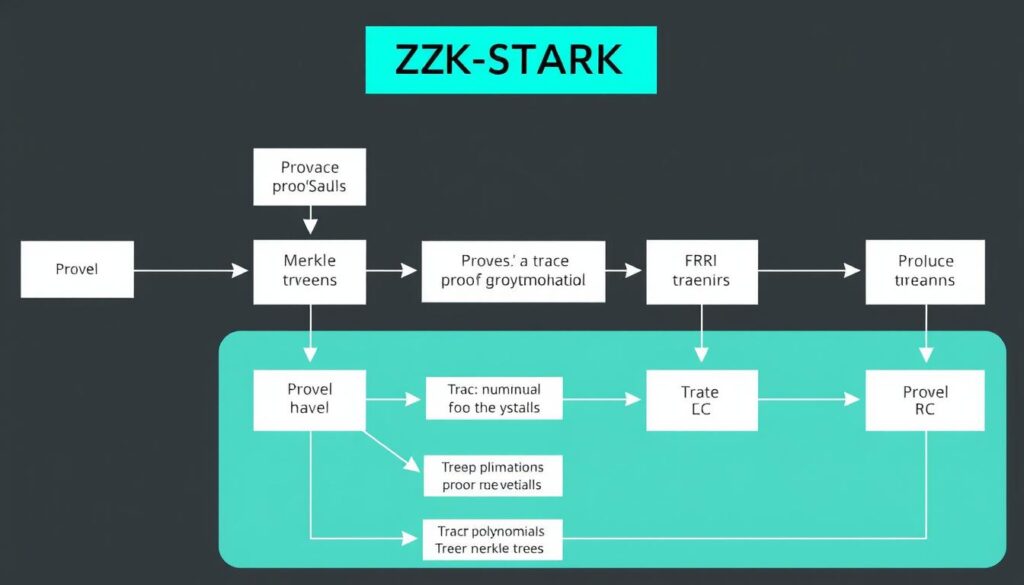
Figure 4: ZK-STARK proof generation and verification process
Explore ZK-STARKs Implementation
Access the StarkWare libraries and documentation to implement quantum-resistant zero-knowledge proofs in your applications.
Privacy-Focused Use Cases
Private Transactions: Learning from Zcash
Zcash pioneered the use of ZK-SNARKs for private transactions on a public blockchain. The protocol allows users to shield transaction details while maintaining verifiability. Here’s how Zcash implements shielded transactions:
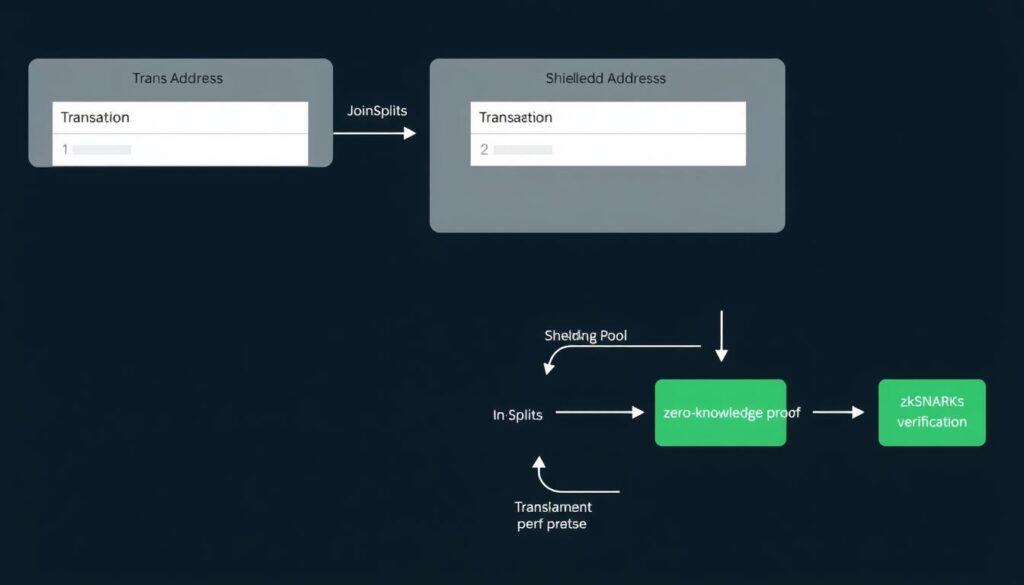
Figure 5: Zcash’s shielded transaction architecture using ZK-SNARKs
The key components of Zcash’s privacy implementation include:
- Payment Addresses: Shielded addresses that hide sender, receiver, and amount
- Note Commitments: Cryptographic commitments to transaction data
- Nullifiers: Unique identifiers that prevent double-spending without revealing the spent note
- ZK-SNARKs: Proofs that validate transactions without revealing details
To implement a similar privacy system in your own blockchain application, you would need to:
- Define a commitment scheme for transaction data
- Implement a nullifier mechanism to prevent double-spending
- Create a circuit for generating ZK-SNARKs that prove transaction validity
- Develop a verification contract that checks proofs on-chain
Identity Verification Without Disclosure
Zero-knowledge proofs enable powerful identity verification use cases where users can prove attributes about themselves without revealing the underlying data. For example, proving you’re over 18 without revealing your birthdate.
// Simplified circuit for age verification
function generateAgeProof(birthdate, currentDate, minimumAge) {
// Calculate age from birthdate and current date
const age = calculateAge(birthdate, currentDate);
// Create a circuit that proves: age >= minimumAge
const circuit = createCircuit(
(private) => {
const calculatedAge = calculateAge(private.birthdate, private.currentDate);
return calculatedAge >= private.minimumAge;
}
);
// Generate the proof with private inputs
return generateProof(circuit, {
birthdate: birthdate,
currentDate: currentDate,
minimumAge: minimumAge
});
}
Scalability Solutions with ZK-Rollups
ZK-Rollups represent one of the most promising applications of zero-knowledge proofs for blockchain scalability. They work by bundling (or “rolling up”) hundreds of transactions into a single proof that can be verified efficiently on-chain.
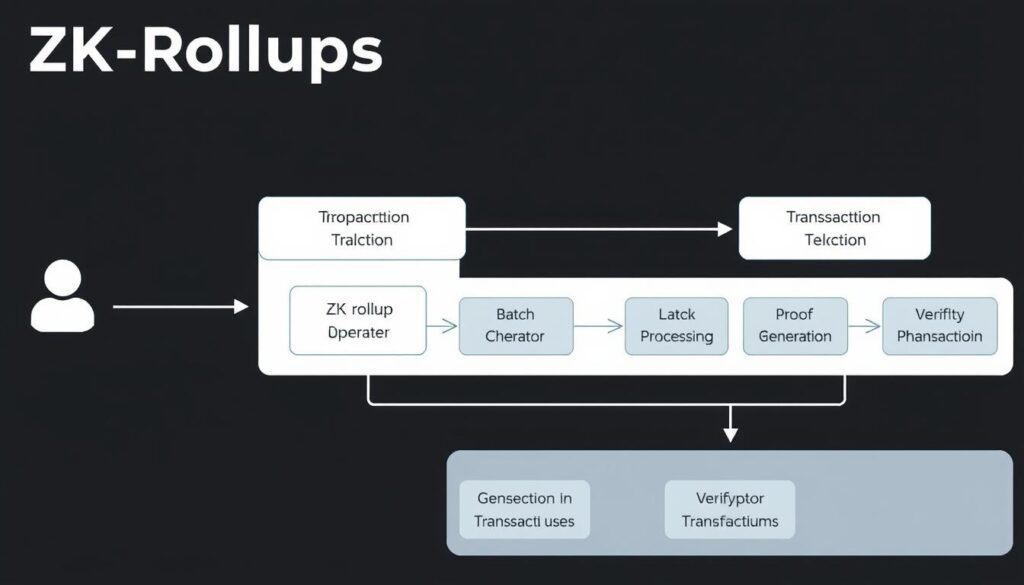
Figure 6: ZK-Rollup architecture for blockchain scalability
How ZK-Rollups Work
The core components of a ZK-Rollup implementation include:
- Off-chain Computation: Transactions are processed off the main chain
- State Transitions: Changes to the system state are computed and compressed
- ZK-Proof Generation: A proof is created that validates all transactions in the batch
- On-chain Verification: The main chain verifies only the proof, not individual transactions
- Data Availability: Transaction data is published on-chain for transparency
Implementing a Basic ZK-Rollup
Here’s a simplified example of a ZK-Rollup contract in Solidity:
// SPDX-License-Identifier: MIT
pragma solidity ^0.8.0;
contract ZKRollup {
// State root represents the current state of the rollup
bytes32 public stateRoot;
// Mapping to track user balances (simplified)
mapping(address => uint256) public balances;
// Verifier contract interface
IZKVerifier public verifier;
constructor(bytes32 _initialStateRoot, address _verifierAddress) {
stateRoot = _initialStateRoot;
verifier = IZKVerifier(_verifierAddress);
}
// Submit a batch of transactions with a ZK proof
function submitBatch(
bytes32 newStateRoot,
bytes calldata transactions,
bytes calldata proof
) external {
// Verify that the proof is valid for the state transition
require(
verifier.verify(stateRoot, newStateRoot, transactions, proof),
"Invalid proof"
);
// Update the state root
stateRoot = newStateRoot;
// Process deposits and withdrawals
processL1Operations(transactions);
emit BatchSubmitted(stateRoot, newStateRoot);
}
// Process Layer 1 operations like deposits and withdrawals
function processL1Operations(bytes calldata transactions) internal {
// Implementation details...
}
// Event emitted when a new batch is submitted
event BatchSubmitted(bytes32 oldStateRoot, bytes32 newStateRoot);
}
interface IZKVerifier {
function verify(
bytes32 oldStateRoot,
bytes32 newStateRoot,
bytes calldata transactions,
bytes calldata proof
) external view returns (bool);
}
Build with ZK-Rollups
Get started with implementing ZK-Rollups for your blockchain application with comprehensive documentation and examples.
Real-world ZK-Rollup Implementations
Several projects have successfully implemented ZK-Rollups to scale Ethereum transactions:
zkSync
A ZK-Rollup solution that supports EVM compatibility, allowing existing Ethereum smart contracts to run with minimal modifications while benefiting from increased throughput and lower fees.
Loopring
A ZK-Rollup protocol focused on decentralized exchange (DEX) functionality, enabling high-throughput trading with the security guarantees of Ethereum’s base layer.
Hermez Network
A scalable payment solution using ZK-Rollups that emphasizes accessibility and low transaction costs while maintaining Ethereum’s security properties.
Tools and Frameworks for ZKP Development
Several libraries and frameworks have emerged to simplify the development of zero-knowledge proof applications. Here are some of the most popular tools:
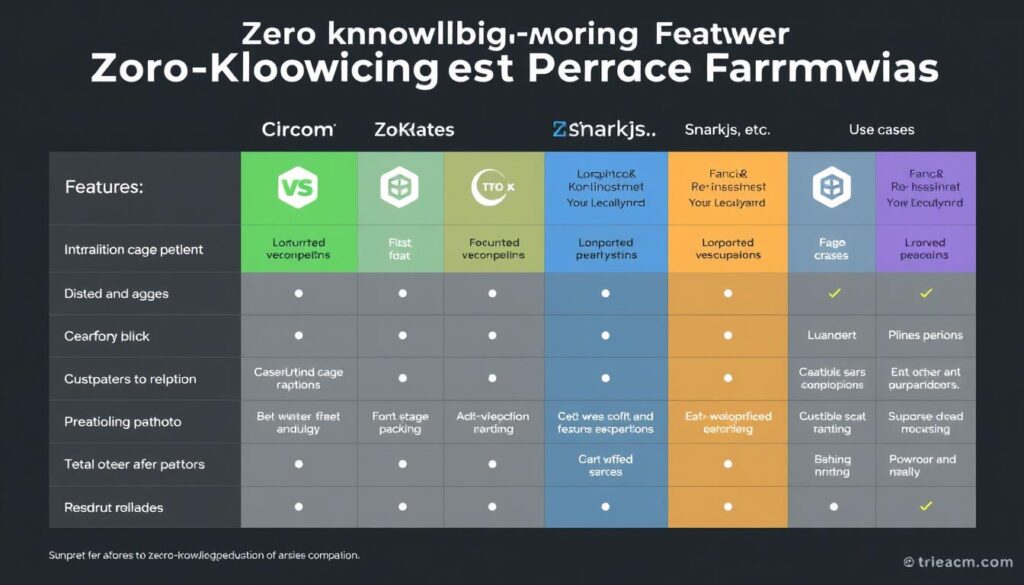
Figure 7: Comparison of popular ZKP development frameworks
Circom and SnarkJS
Circom is a domain-specific language for writing arithmetic circuits, while SnarkJS is a JavaScript implementation of ZK-SNARK generation and verification. Together, they provide a comprehensive toolkit for ZKP development.
// Example Circom circuit for range proof
pragma circom 2.0.0;
template RangeProof(n) {
// Public inputs
signal input max;
// Private inputs
signal input value;
// Ensure value is within range [0, max]
signal lt = LessThan(n)([value, max + 1]);
lt === 1;
// Additional constraints to ensure value >= 0
signal valueSquared
ZoKrates
ZoKrates is a toolbox for ZK-SNARKs on Ethereum. It includes a high-level language for writing verification circuits, a compiler, and tools for generating and verifying proofs.
// ZoKrates example for hash preimage verification
def main(private field preimage, public field hash) -> bool:
field computed_hash = sha256packed(preimage)
return computed_hash == hash
Platforms for ZKP Development
Aleo
A platform for building private applications using zero-knowledge proofs. Aleo provides a programming language called Leo that simplifies the development of privacy-preserving applications.
Mina Protocol
A lightweight blockchain that uses recursive ZK-SNARKs to maintain a constant-size blockchain regardless of transaction volume, enabling verification on resource-constrained devices.
StarkWare
Offers StarkEx and StarkNet platforms for developing scalable applications using ZK-STARKs, with a focus on high throughput and reduced gas costs.
Start Building with ZKP Tools
Access comprehensive development resources for building privacy-preserving and scalable blockchain applications.
Challenges in Implementing Zero-Knowledge Proofs
Advantages
- Enhanced privacy for sensitive transactions
- Significant scalability improvements
- Reduced on-chain data requirements
- Compatibility with existing blockchain infrastructure
- Growing ecosystem of development tools
Challenges
- High computational requirements for proof generation
- Complex trusted setup procedures for some ZKP types
- Specialized knowledge required for implementation
- Gas costs for on-chain verification
- Evolving standards and best practices
Computational Overhead
Generating zero-knowledge proofs is computationally intensive, often requiring specialized hardware for production applications. This can be a barrier to entry for smaller projects or developers with limited resources.
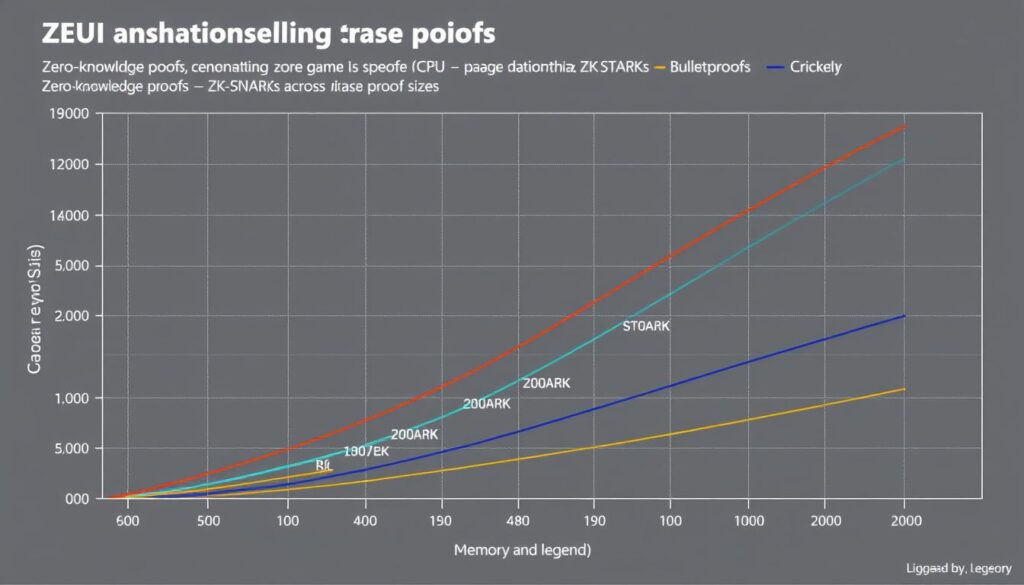
Figure 8: Computational requirements for different ZKP types
Trusted Setup Considerations
ZK-SNARKs require a trusted setup phase where cryptographic parameters are generated. If this process is compromised, it could potentially allow the creation of false proofs. Strategies to mitigate this risk include:
- Multi-party computation (MPC): Involving multiple parties in the setup process
- Transparent setups: Using ZK-STARKs which don’t require trusted setups
- Updatable setups: Allowing parameters to be updated over time
Audit and Security Considerations
ZKP implementations require thorough auditing due to their cryptographic complexity. Common security considerations include:
- Circuit vulnerabilities: Flaws in the constraint system design
- Implementation bugs: Errors in the proof generation or verification code
- Parameter management: Secure handling of cryptographic parameters
- Side-channel attacks: Information leakage during proof generation
Future Trends in Zero-Knowledge Proofs
Figure 9: Evolution and future trends in zero-knowledge proof technology
Hybrid Scaling Solutions
The future of blockchain scaling likely involves hybrid approaches combining zero-knowledge proofs with other scaling techniques:
- ZK-Rollups + Sharding: Combining the throughput benefits of both approaches
- Validiums: ZK-Rollups with off-chain data availability for even greater scalability
- Recursive Proofs: Proofs that verify other proofs, enabling exponential scaling
Standardization Efforts
As ZKP technology matures, standardization efforts are emerging to ensure interoperability and security:
- ZKProof: An open industry academic initiative to standardize ZKP implementations
- EIP Standards: Ethereum Improvement Proposals for ZKP verification and integration
- Cross-chain Standards: Protocols for ZKP verification across different blockchains
Emerging Applications
Private DeFi
Decentralized finance applications that preserve transaction privacy while maintaining regulatory compliance through selective disclosure.
Verifiable Computation
Using ZKPs to outsource complex computations and verify results, enabling more sophisticated on-chain applications.
Cross-chain Bridges
Secure and efficient cross-chain communication using ZKPs to verify state transitions between different blockchain networks.
Figure 10: Future applications of zero-knowledge proofs in blockchain ecosystems
Conclusion: Implementing ZKPs in Your Blockchain Projects
Zero-knowledge proofs represent a powerful tool for addressing two of blockchain’s most significant challenges: privacy and scalability. By allowing verification without revealing underlying data, ZKPs enable a new generation of applications that preserve user privacy while maintaining the transparency and security benefits of blockchain technology.
As we’ve explored in this guide, implementing ZKPs requires understanding the different proof systems available, choosing the right tools and frameworks, and addressing challenges related to computation, trusted setups, and security. Despite these challenges, the benefits of ZKPs make them an essential technology for blockchain developers looking to build more private, scalable, and user-friendly applications.
Figure 11: Implementation roadmap for integrating ZKPs into blockchain projects
Ready to Implement Zero-Knowledge Proofs?
Get comprehensive resources, code examples, and development tools to start building privacy-preserving and scalable blockchain applications today.
Frequently Asked Questions
What’s the difference between interactive and non-interactive zero-knowledge proofs?
Interactive zero-knowledge proofs require back-and-forth communication between the prover and verifier, while non-interactive proofs (like ZK-SNARKs and ZK-STARKs) can be verified without further interaction after the proof is generated. Non-interactive proofs are more suitable for blockchain applications since they can be verified by smart contracts without requiring the prover to be online.
How do ZK-Rollups compare to Optimistic Rollups for scaling?
ZK-Rollups use zero-knowledge proofs to validate transaction batches, providing immediate finality once the proof is verified on-chain. Optimistic Rollups assume transactions are valid by default and rely on fraud proofs during a challenge period. ZK-Rollups typically offer faster finality and stronger security guarantees but require more computational resources for proof generation. Optimistic Rollups are generally simpler to implement but have longer withdrawal periods due to the challenge window.
Are zero-knowledge proofs quantum-resistant?
It depends on the type of zero-knowledge proof. ZK-SNARKs rely on elliptic curve cryptography, which is vulnerable to quantum computing attacks. ZK-STARKs, on the other hand, use hash functions and information-theoretic techniques that are believed to be quantum-resistant. As quantum computing advances, ZK-STARKs may become the preferred option for long-term security, despite their larger proof sizes.
What are the gas costs associated with verifying ZK proofs on Ethereum?
Verifying ZK-SNARK proofs on Ethereum typically costs around 500,000 to 800,000 gas, depending on the complexity of the circuit. ZK-STARK verification is more expensive, often requiring several million gas. However, when amortized across hundreds or thousands of transactions in a rollup batch, the per-transaction cost becomes very low, making ZK-Rollups one of the most gas-efficient scaling solutions available.
How can I ensure the security of my ZKP implementation?
To ensure the security of your ZKP implementation: 1) Use established libraries and frameworks rather than implementing cryptographic primitives yourself; 2) Conduct thorough security audits by specialists in zero-knowledge cryptography; 3) For ZK-SNARKs, ensure the trusted setup is performed securely, preferably through a multi-party computation ceremony; 4) Test extensively with different inputs, including edge cases; and 5) Stay updated with the latest security research and best practices in the ZKP community.


No comments yet